Use For VPN
- VPN to connect to home networks to transfer photos, documents and Downloading Files etc.
- Bypass geographic location prohibited on websites and streaming video and audio.
- Saftey and Security and use for public wifi
- VPN through Access sites when you're abroad
- Hide Your Browsing Activity From Your ISP (Internet Service Provider) and Local Network and Location.
Benefits of a VPN (Virtual Private Network)
- Security improve and encryption
- Hide of your private information
- Disguising your whereabouts
- Secure data transfer
- Access to regional content
- Reduce support costs
- Bypass Blockers and Filters
- Remote Access and File sharing
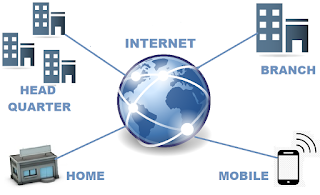
1.Remote Access VPN
Remote Access VPN through user connect to a private network and access resources and services. Employee is use remotely acces to company and home network. primarily VPN use services to bypass geo regional restrictions on the Internet and access blocked websites.The connection between the private network and user occurs through the Internet and the connection is secure and private. Remote Access VPN is useful for business users and home users both.
2.Site to Site VPN
Site to Site VPN is also called as Router to Router VPN and is commonly used in the large and corporate companies. Companies and organizations, and branch offices in different locations use to Site-to-site VPN and connect the network of one office location to another office location.
Site to site VPN create bridge between the networks at geographically distant offices and connect through Internet and private,securecommunication between the networks .
Types of Virtual Private Network (VPN) Protocols:
- Point–to–Point Tunneling Protocol (PPTP)
- Internet Protocol Security (IPSec)
- Layer 2 Tunneling Protocol (L2TP)
- SSL and TLS
- OpenVPN
- Secure Shell (SSH)
Point–to–Point Tunneling Protocol (PPTP)
Point-to-Point Tunneling Protocol (PPTP) creates a tunnel and encapsulates the data packet. Point-to-Point Protocol (PPP) use for encrypt the data between the connection. PPTP is one of the most widely used VPN protocol and supported on Windows, Mac and Linux.
Internet Protocol Security (IPSec):
Internet Protocol Security(IPSec) is used to secure Internet communication across an IP network. IPSec secures Internet Protocol encrypts each data packet during the connection and communication by authenticating the session.
IPSec operates in two modes :
(1)Tunneling mode
(2) Transport mode
This two mode protect data transfer between two different networks .The tunneling mode encrypts the entire data packet and the transport mode encrypts the message in the data packet. IPSec can also be used security protocols and Secure Internet communication across an IP network.
Layer 2 Tunneling Protocol (L2TP):
Layer 2 Tunneling Protocol (L2TP) Tunneling Protocol is a tunneling protocol that is usually combined with another VPN security protocol like IPSec to create a highly secure VPN connection. L2TP generates tunnel between two L2TP connection points and IPSec protocol encryption the data and maintains secure connection between the tunnel.
SSL and TLS:
Secure Sockets Layer (SSL) and Transport Layer Security (TLS) generate a VPN connection where the web browser acts as the client and user access is restricted to specific applications instead of entire network. The Online shopping websites uses Secure Sockets Layer (SSL) and Transport Layer Security (TLS).SSL web browsers easy to switch and with almost no action required from the user as web browsers come integrated with Secure Sockets Layer (SSL) and Transport Layer Security (TLS). SSL connections have https in the initial of the URL Inceptive of http
OpenVPN:
OpenVPN is open source VPN that is useful for creating Point to Point and Site to Site connections. It uses a custom security protocol based on Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocol.
Secure Shell (SSH):
Secure Shell (SSH) generates the VPN tunnel through which the data transfer happens and also ensures that the tunnel is encrypted. SSH connections are generated by a SSH client and data is transferred from a local port on to the remote server through the encrypted tunnel generate.
Free VPN Service Provide Software
- ProtonVPN Free
- Hide.me
- TunnelBear
- Speedify
- ZoogVPN
- Windscribe
- Touch VPN
- Hotspot Shield Free VPN
Paid VPN Services Provide Software
- NordVPN
- Avast Secureline VPN
- ExpressVPN
- Surfshark
- CyberGhost VPN
- AVG Secure VPN
- IPVanish
- PureVPN
- VyprVPN
- Private Internet Access





0 Comments